If you’ve just wired up an industrial cellular router, logged into the dashboard, and saw the green “Connected” light, you might think the job is done. But for field engineers dealing with remote pump stations or high-vibration factory floors, “connected” isn’t enough. You need optimized reliability.
You need a connection that stays alive when extreme temperatures hit 70°C, or when a massive forklift drives by and creates a wall of electromagnetic interference (EMI).
📋 In this advanced field guide, we skip the basic manual and cover:
- Why “Signal Bars” (RSSI) are lying to you: The real difference between RSSI and SINR.
- MTU Tuning: How to stop OpenVPN overhead from bottlenecking your router.
- Hardware Reality Check: Why consumer SIMs and cheap enclosures fail in SCADA applications.

Beyond the Bars: Why RSSI is Lying to You (Signal Optimization)
Forget router software for a moment. The most critical configuration happens outside the box. A weak or noisy cellular signal is a performance ceiling no software setting can break.
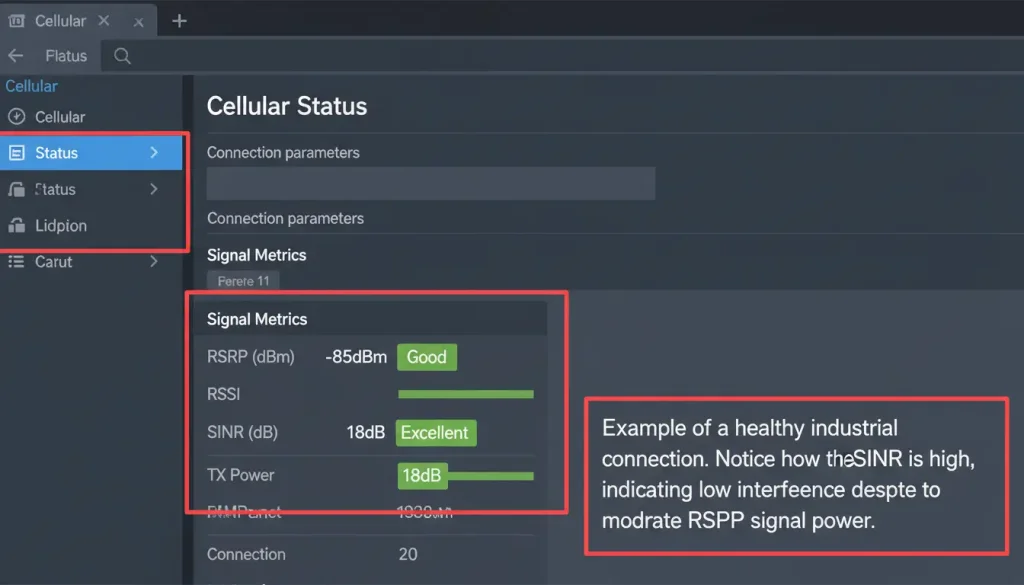
Most technicians look at the “Signal Bars” (RSSI) on the dashboard and walk away. This is a massive mistake in industrial IoT. Signal quantity does not equal signal quality. You can have full bars and zero data throughput if the noise floor in your factory is too high. To truly perform a rock-solid configurtion (and yes, getting the details right is that important), you must look at RSRP and SINR.
- RSRP (Reference Signal Received Power): This is the actual strength of the specific LTE signal you care about. If it’s worse than -105 dBm, your connection is barely breathing.
- SINR (Signal-to-Interference-plus-Noise Ratio): This is the holy grail of cellular metrics. It measures clarity.A Signal to Interference Plus Noise Ratio of 20 decibels is like driving on an open highway. A Signal to Interference Plus Noise Ratio of 3 decibels is, like being stuck in a traffic jam when there is a thunderstorm.
Antenna Selection is a Configuration Choice
Picking the antenna is the first thing you need to do. It is also the important step when it comes to setting up your equipment.
The antennas that are used for industry and have a gain can really change how well your MIMO system works. Your MIMO system, which stands for Multiple Input, Multiple Output is affected by the type of antenna you choose.
Directional vs. Omni-Directional: This isn’t about better or worse, but application. An omni antenna is great if the router’s location is central or if it’s moving (e.g., on a vehicle). A directional (Yagi) antenna is for fixed installations where you can point it precisely at the distant cell tower. The gain trade-off is crucial for optimizing your RSRP.
Cable Loss Matters: That thin cable that came with the box is not doing your signal any good. It is actually making it weaker. If you have to run the cable for more than a meter especially if it is inside a metal cabinet you should use a cable. You should use a loss coaxial cable, like LMR-400. The connector on the cable such as SMA has to be the type as the ports, on your router. This is a thing to check but people often forget to do it.
| Scenario / Challenge | Recommended Antenna Type | Key Considerations |
| Indoor Cabinet, Severe Metal Shielding | External Omni mounted outside the cabinet or on the roof. | Cable length and penetration loss. Avoid placing antenna inside metal enclosures. |
| Fixed Remote Site, Distant Cell Tower | Directional (Yagi) pointed precisely at the tower. | Requires alignment. Higher gain improves signal-to-noise ratio in low-coverage areas. |
| Mobile Asset (Vehicle, Machinery) | Magnetic-mount Omni on roof or exterior. | Vibration resistance, secure cable routing. |
| General Outdoor Enclosure / Kiosk | Stubby Omni or Small Panel antenna. | Connector weatherproofing is critical (use drip loops and sealant). |

Smart Dual-SIM Failover & Signal Switching Logic
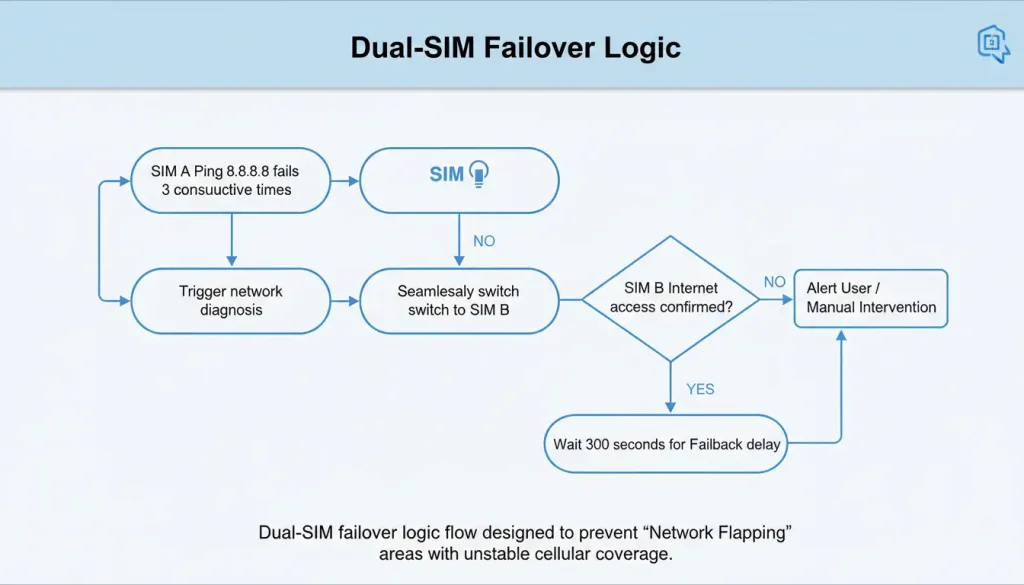
The biggest problem for places that’re far away is something called the “silent drop”. This is what happens when Operator As tower is really busy or their network connection is not working. The cellular module can still find the local radio signal. A regular router will keep trying to stay connected, to this link that is not working while your SCADA system will stop waiting and time out.
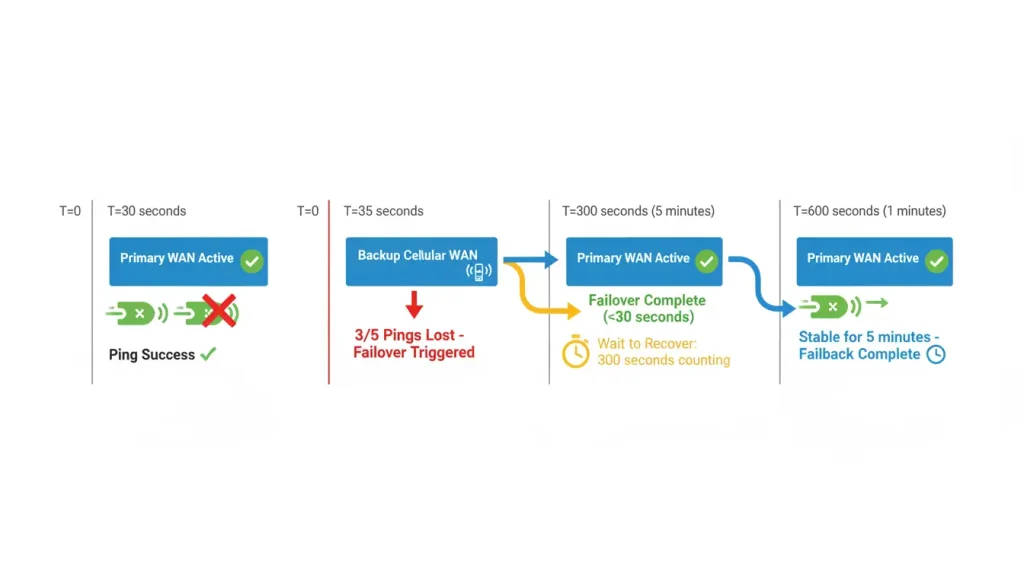
The great thing about an industrial router is that it can switch to a backup link when the main one fails. But if this switcing process happens in a clumsy way, the auto-switch latency is actually worse than having a slow link.
Smart Failure Detection (The ICMP Logic)
Don’t rely solely on the “WAN Link Down” trigger. A cable can be plugged in, or a radio link established, but still lead to a dead network. You must use the “Ping Probe” or “Gateway Ping” feature to verify actual internet transit.
- How to Configure: Set the router to ping a highly stable IP address—like your company’s primary DNS server, your HQ VPN gateway, or a reliable public IP (8.8.8.8)—every 10 seconds.
- The Trigger Condition: Configure the rule to trigger failover if, for example, 3 out of 5 pings fail. This detects real service outages, not just temporary physical packet loss.
- Cellular Backup Link Priority & Failback: Equally important is how it switches back. You don’t want it “flapping” between links. Set a “Wait to Recover” period (e.g., 300 seconds) where the router must see the primary link stable for a full 5 minutes before failing back.
| Feature | Configuration Item | Recommended Setting / Strategy | Purpose |
| Failover | Detection Method | Ping Probe to a stable IP (e.g., HQ server). | Detects real network outage, not just physical link drop. |
| Trigger Condition | 3 failures out of 5 consecutive pings. | Avoids false triggers due to temporary packet loss. | |
| Recovery Hold-off | Wait 300 seconds after primary link recovers before switching back. | Prevents link “flapping” during an unstable recovery period. |
The VPN Performance Trap: Encrypted Throughput vs. Overhead
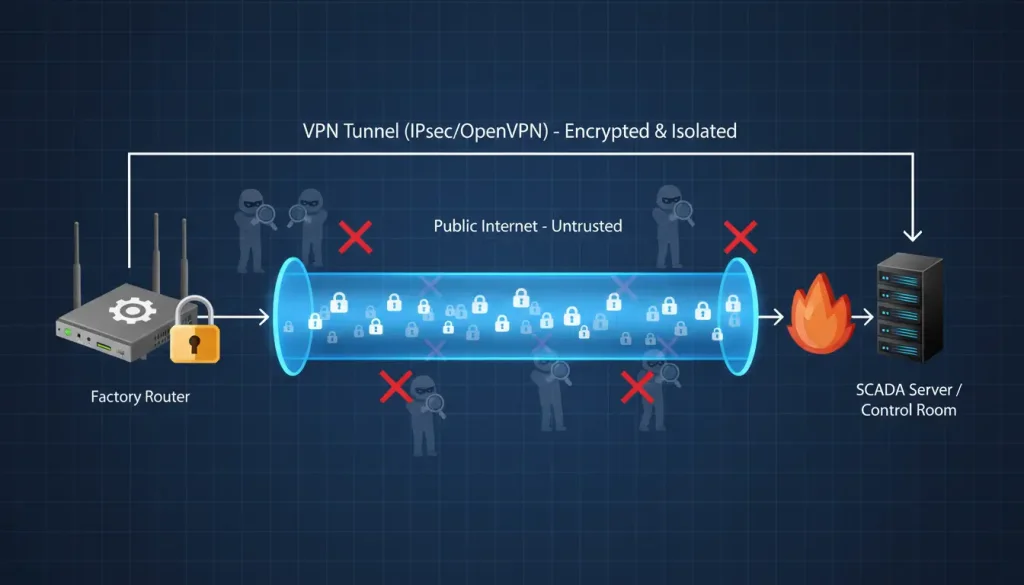
Using a Virtual Private Network (VPN) to your headquarters is practically mandatory for industrial security. However, encryption brings a heavy cost: Bandwidth Overhead. Many engineers complain that their cellular VPN is “too slow,” assuming the carrier is throttling them. The truth? It’s rarely a bandwidth issue—it’s a Fragmentation issue.
OpenVPN vs IPsec Performance
Choosing the right protocol dictates your CPU load.
- IPsec is what people usually use for site-to-site tunnels. It works exceptionally fast on hardware-accelerated routers. If you want to connect a site that is not moving around to your main network all the time IPsec is a good option.
- OpenVPN is incredibly flexible and great for traversing complex firewalls, but it carries a higher TCP/UDP overhead and makes the router’s CPU work harder, which can limit your maximum throughput on lower-end devices.
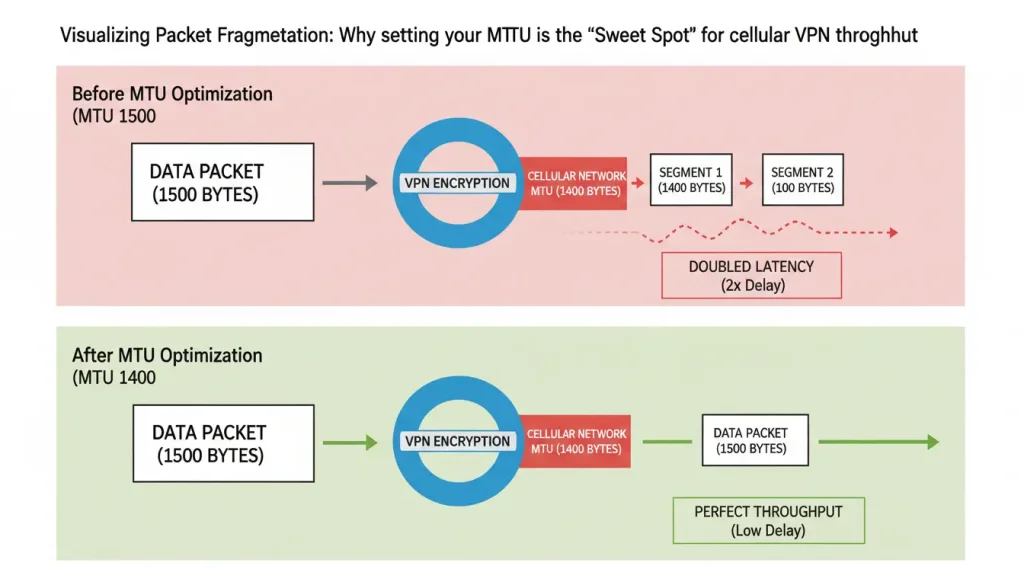
The MTU Fix: Curing the Slow VPN
This is a classic culprit behind a sluggish tunnel. Cellular networks (due to standard 3GPP specifications) naturally have a lower Maximum Transmission Unit (MTU) than standard wired Ethernet because of the GTP tunneling happening inside the carrier’s core network.
If your VPN packet is too large (e.g., the standard 1500 bytes), the cellular modem is forced to split it into two fragments. This fragmentation is really bad for performance. It makes your latency much worse, in fact it is twice as bad. The performance of the system is affected by this fragmentation. The latency of the system is doubled because of this fragmentation.
- The Actionable Fix:When you are working with your VPN settings you need to change the MTU to 1400 or even 1350 and your MSS, which is the Maximum Segment Size to 1360. You should test it. Make adjustments as needed. This one change is often overlooked,. It makes sure your encrypted data fits perfectly into the LTE frame without getting broken up.
| VPN (IPsec) | Configuration Item | Recommended Setting / Strategy | Purpose |
| Phase 1 Encryption | AES-256, SHA-256, DH Group 14. | Strong security with good performance balance. | |
| Phase 2 Encryption | AES-128-GCM. | Efficient encryption, lower CPU overhead. | |
| MTU/MSS | MTU=1400, MSS=1360. | Prevents packet fragmentation over cellular networks. | |
| Keep-Alive | Enabled, interval of 20 seconds. | Maintains tunnel state and allows fast dead peer detection. |
Band Locking & Carrier Aggregation: Forcing Stability in the Chaos
In crowded cities where they are building a lot or in factories with a lot of machines cell towers are often very busy. The industrial router you are using can work with different LTE bands, such, as Band 2 Band 4 Band 12 Band 13 and so on. When it is set to “Auto” mode the industrial router will connect to the signal it can find without thinking about it.
The problem is that the strongest signal, like a frequency Band 12 that goes through walls easily is usually very crowded. Band 12 is the signal. A weaker signal, like a frequency Band 4 might be totally free.
The router is always switching between Band 12 and Band 4 trying to find the signal. This constant switching, between Band 12 and Band 4 creates a lot of jitter. Band 12 and Band 4 are the signals that the router is switching between.
Hardware Watchdogs and ICMP Keep-Alive: The Auto-Reboot Lifeline
Picture this: Your router is on a utility pole in a desert facility with no one. If the modem freezes because of a problem with the carrier fixing it needs an engineer to drive 4 hours to get there and 4 hours back. That is a $500 truck trip, for a task that takes 5 seconds. You have to set the device to fix itself automatically.
- The Hardware Watchdog Timer: This thing is not a computer program it is a part that needs a regular signal from the routers system. The signal is like a heartbeat. If the system stops working because of much information or a surge of power the watchdog turns off the power, for a very short time to make the system start again from the beginning. You should turn the watchdog on.
- ICMP Keep-Alive Logic: Don’t just reboot the whole router if the internet goes down. Set a granular rule: “If the router cannot ping the gateway for 15 consecutive minutes, restart the cellular module only.” This clears “stuck” PDP contexts with the local cell tower without dropping the local LAN network or disrupting local PLC-to-PLC communication.
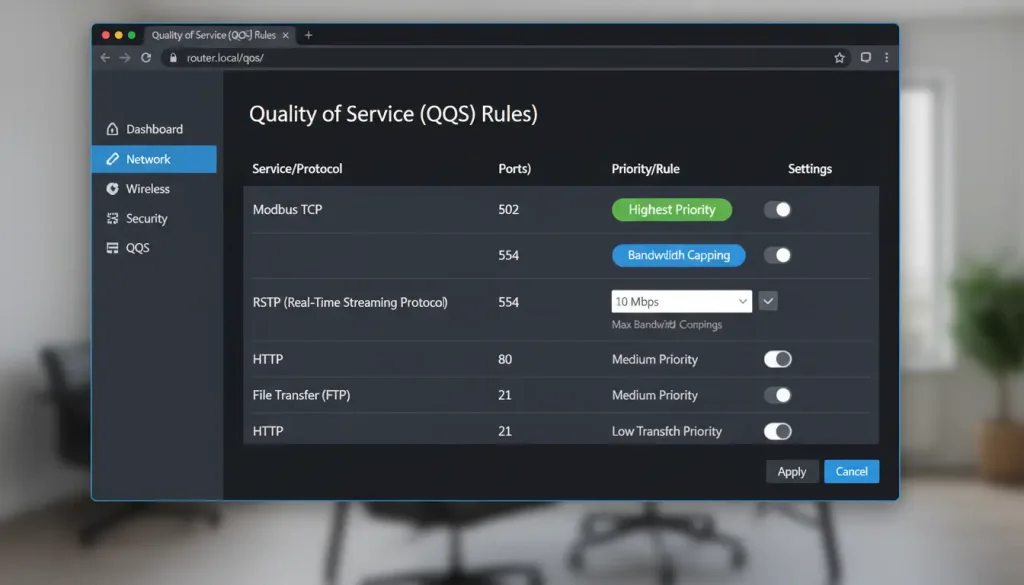
Traffic Control: Bandwidth Shaping and QoS for Mission-Critical Data
Industrial cellular data is not just costly because you use a lot of it. It is also costly because you can get charged extra for going over your limit or your data speed can be slowed down. You need to make sure the things you do get done while the things that are not important are blocked. Industrial cellular data is something you have to think about carefully.
Think of Quality of Service as your traffic control system. This Quality of Service decides which data packets get to go when the road gets crowded. We should forget about using High, Medium, Low” tags that are based on IP addresses. Instead we need to create rules, for Quality of Service based on what the applicationsre actually doing.
- Priority 1: Control Commands (The Emergency Vehicles). PLC polling, Modbus TCP, and OPC UA. If a “Stop” command is delayed, machinery breaks. Make a strict rule that gives traffic on Port 502 (Modbus) the absolute highest priority.
- Priority 2: Alarm and Event Packets. These are tiny packets, but they play a massive role. Tag protocol-specific notifications so they jump the queue instantly when an anomaly is detected.
- Priority 3: Live Video for Monitoring. This is a constant flow of traffic that will easily choke your emergency vehicles. Set a QoS rule to throttle its maximum bandwidth—cap it at 60-70% of your available uplink.
- Priority 4: The Freight (File Transfers & Logs). System log uploads and firmware updates are heavy but not time-sensitive. Schedule time-based bandwidth shaping rules to only allow these transfers during off-peak hours, like 2:00 AM.
| Traffic Category | Priority Level | Protocol Examples | Optimization Strategy |
| Mission-Critical | Highest | Modbus TCP, MQTT | Minimal latency, guaranteed bandwidth. |
| Safety & Alarms | High | SNMP Traps, Alarms | Instant queue jumping. |
| Visual Monitoring | Medium | RTSP, HTTP Video | Bandwidth capping (Throttling). |
| Background Data | Lowest | Syslogs, Firmware | Off-peak scheduling only. |
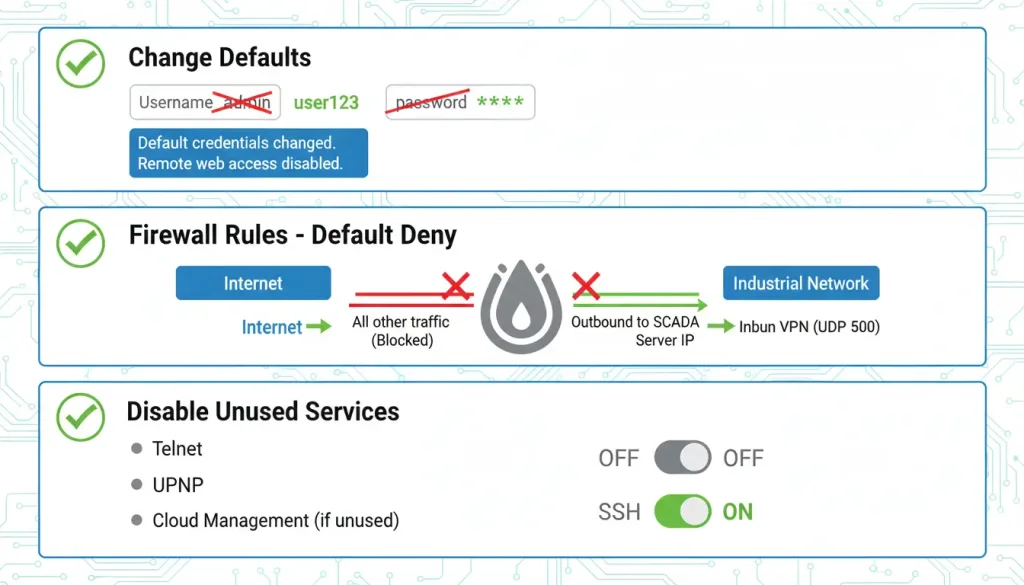
Security and the Often-Ignored Hardware Environment
A compromised router is an unstable router. Misrouted traffic or malware scanning will consume your CPU and bandwidth rapidly.
The First 5 Minutes: Changing Defaults. Change the default admin username. Hackers try “admin” and “password” within seconds of finding a public IP. Disable access to the web management interface from the WAN side. Firewall Rules: Building a Moat. Deny all traffic on the internet side. Only allow INBOUND traffic from your specific HQ public IP addresses to the specific port needed for your VPN (e.g., UDP 500 for IPsec). Turn off UPnP—it is a convenience feature for home gaming that creates massive security holes in industrial settings.
The Physical Install
The best software configuration is not going to fix a hardware deployment. When we talk about things we are talking about things that are made to work well in the real world. The best software configuration and a terrible hardware deployment do not go together. Industrial means things have to work when people actually use them.
- Power: In plants, voltage sags and spikes are common. Use a regulated, industrial-grade DC power supply. For mission-critical nodes, use a small DC-UPS.
- Heat: Industrial routers can handle high temperatures but they still need some air. If you put one at the top of a sealed box in the sun it is going to get too hot. You have to make sure there is some space, for air to get in and out. Industrial routers need this space to breathe. They will not work properly. Leave some room for air to move around the router.
- DIN-Rail: That secure click onto the 35mm DIN rail prevents vibration from loosening your SMA antenna connections over time on a factory floor.
| Parameter | Specification | Practical Implication for Configuration & Deployment |
| Cellular Bands | LTE Cat1, B1/B3/B5/B7/B8/B20 | Covers major bands across EMEA/Asia. Verify compatibility with your local carrier. |
| Peak Data Rates | 10 Mbps Downlink / 5 Mbps Uplink | Sets a realistic ceiling for application design. Ideal for telemetry. |
| Network Interfaces | 4 x LAN (10/100), 1 x WAN, Dual-SMA | Flexible for multi-device networks and essential for external antennas. |
| Core Routing | 4G to LAN/WiFi, WAN to LAN | Enables use as primary cellular gateway or wired backup. |
| Industrial Protocols | Modbus TCP Gateway, MQTT Client | Allows direct integration into automation platforms. |
| Power Input | 9-24V DC, Terminal Block | Wide range accommodates most industrial 12V or 24V DC systems. |
| Operating Temp | -40°C to +85°C | Validates deployment in unheated enclosures or harsh outdoor environments. |
Real-World Scenarios: Designing for the Application
Let’s walk through the configuration mindset for two entirely different needs.
Scenario 1: The Remote Solar-Powered Water Tank Monitor
- Priority: Ultra-low power use, reliable daily data bursts, instant alarm transmission.
- Execution: Use a small external omni antenna on a mast. Configure the exact private APN from your carrier. Turn off any “always-on” VPN keep-alives if not actively polling to save battery. Set QoS Rule #1 to prioritize the RTU’s IP address to the alarm server.
Scenario 2: In-Factory Mobile AGV (Automated Guided Vehicle)
- Priority: Continuous, low-latency connectivity as it moves through WiFi dead zones.
- Execution: Mount two external omni antennas on opposite sides of the AGV for spatial diversity. Set WiFi as the primary WAN, with cellular as the aggressive failover. Lock the LTE band to a frequency less affected by factory motors. Lock the firewall tightly to only allow outbound connections to the AGV fleet server.
Scenario 3: Smart Healthcare & Remote Patient Care
- Priority: Regulatory compliance (HIPAA/GDPR) and “Zero-Drop” reliablity for life-saving data.
- Execution:
- The Stakes: This market is growing at 15–18% CAGR, reaching $150B by 2030. In hospitals, 40–50% of monitoring is now wireless.
- Configuration: Implement 4G/wired smart backup to ensure vital signs (ECG, oxygen) are never interrupted. Use the 300-second Failback rule to ensure that once a stable link is found, it stays there.
- Security: Encrypt all data in transit using IPsec. Use Network Segregation to keep patient data separate from the hospital’s guest WiFi.
- Impact: Proper configuration here can reduce hospital readmissions by 25–30% and save 2,000 nursing hours per year.
Maintenance and the “Self-Healing” Router
A router in a desert or a hospital basement should fix itself.
- Hardware Watchdog: Enable this to hard-reboot the device if the OS freezes.
- ICMP Keep-Alive: If pings fail for 15 minutes, restart the cellular module only. This clears “stuck” carrier sessions without dropping the local LAN.
- QoS Priority:
- P1: Modbus/Control Commands (The Emergency Vehicles).
- P2: Alarms (The First Responders).
- P3: Video/Logs (The Freight).
The Field Engineer’s Performance Checklist
You’ve clicked “Apply.” Now what? You must validate the setup before leaving the site.
| Validation Step | Feature Tested | Action to Perform | Expected Result / Benchmark |
| 1. Simulate Outage | Dual-SIM Failover | Unplug Primary WAN / Remove SIM 1. | Router switches to Backup link in < 30 seconds without freezing. |
| 2. Check Packets | VPN MTU Setting | Ping HQ server with large packets (1400 bytes). | 0% fragmentation; steady low-latency replies. |
| 3. Read Signals | Antenna & Interference | Check diagnostics page for RSRP and SINR. | SINR must be > 10 dB. If lower, relocate the antenna. |
| 4. Test Self-Heal | Watchdog / Keep-Alive | Block the router’s ping IP at the firewall level. | Router should detect failure and auto-reboot the modem in 15 mins. |
| 5. Network Scan | Security / Firewall | Run an external port scan against the router’s WAN IP. | All non-VPN ports (HTTP, Telnet, SSH) should show as “Stealth/Closed”. |
The Final Step: Proving Your Configuration Works
You have clicked Apply. Now what happens? You need to validate the information. The Apply button has been clicked. It is time to validate.
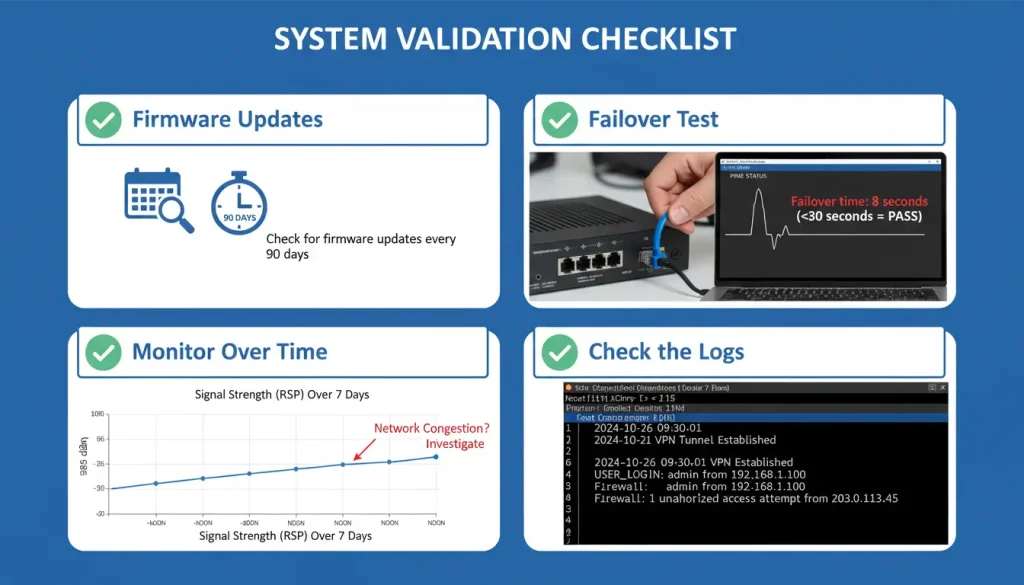
You’ve clicked “Apply.” Now what? You must validate.
- Firmware Updates: Mark your calendar. Check the manufacturer’s website quarterly for firmware updates. These fix bugs, close security holes, and sometimes improve modem performance. Always test on one unit first before a fleet-wide rollout.
- Test the Failover: Unplug the primary WAN. Use a continuous ping from a device on the router’s LAN to an internet address. Measure the time of disruption. A good industrial router will switch in under 30 seconds. Do this during a planned maintenance window.
- Monitor Over Time: Don’t just set and forget. Use the router’s built-in tools (if available) or a simple script to log signal strength (RSRP, SINR) and cellular data usage over a week. Spot trends—does performance dip at noon every day? (Could be network congestion).
- Check the Logs: Once a week, glance at the system log. Look for repeated VPN reconnections (indicating instability) or firewall blocks (indicating misconfigured devices).
Common Configuration Mistakes (and How to Avoid Them)
Even experienced engineers make these errors. Here’s what to watch for:
- Using the wrong APN – Double‑check with your carrier. A misconfigured APN can work, but at reduced speed or with unstable connections.
- Forgetting to update firmware – Manufacturers release updates that fix bugs and improve modem performance. Check quarterly.
- Skipping the site survey – Deploying without checking signal strength first leads to “it worked in the office, but not in the field” headaches.
- Over‑terminating the network – Adding termination resistors on star‑wired RS485 segments (if using a serial router) causes reflections. Read the manual.
- Ignoring the logs – The router’s log often shows the root cause of intermittent issues (e.g., “VPN reconnecting every hour”). Check it periodically.

The Ultimate Fix: Start with the Right Hardware
You can spend hours tweaking MTU sizes and forcing radio bands, but if your router’s CPU can’t handle encrypted VPN tunnels, or if its housing isn’t built for extreme EMI, your network will still fail. Software configuration cannot fix hardware limitations.
For system integrators building networks for Factory Automation (PLCs), Remote CCTV, or Kiosks, we engineered the [Valtoris VT-LTE400].
Instead of a basic “box that provides internet,” the VT-LTE400 gives you:
- 4x LAN Ports & DIN-Rail Mount: Directly connect multiple PLCs or IP cameras inside your control cabinet.
- Wi-Fi Bridge Mode: Easily extend existing factory networks to hard-to-reach machines.
- True Industrial Tolerance: Wide operating temperature and EMI-shielded metal enclosure.
Stop troubleshooting offline nodes. 👉 Contact Our Engineers to review your current network architecture for free.
(This guide references industry standards including GSMA and 3GPP specifications. Always consult your device manual for specific settings.)
Frequently Asked Questions
Q1: Why can’t I remotely access my PLC behind the cellular router even though it has internet access?
A: This is almost always due to CGNAT (Carrier-Grade NAT). Most consumer cellular carriers assign your router a private, non-routable IP address, which blocks inbound traffic. To remotely access your SCADA systems, you must either request a Static Public IP from your carrier (usually via an M2M data plan) or configure the router to establish an outbound VPN tunnel (like OpenVPN or IPsec) to your central server.
Q2: Can I use a standard smartphone SIM card in an industrial router?
A: Technically yes, but it is highly discouraged. Consumer SIMs often have roaming restrictions, dynamic IPs, and terms of service that strictly prohibit continuous machine-to-machine (M2M) polling. For industrial automation, always source dedicated IoT/M2M SIM cards and configure custom APNs to ensure uninterrupted data flow and prevent sudden carrier blocks.
Q3: How do I integrate the 4G router as a backup WAN for my existing corporate firewall without causing double-NAT issues?
A: If you are connecting the cellular router behind a main firewall, such as Cisco or Fortinet, you should set the cellular router to IP Passthrough (or Bridge) Mode. This turns off the router’s internal DHCP and NAT and sends the carrier’s IP straight to the WAN port on your main firewall.
➔ To compare routers that natively support advanced failover and Passthrough modes, review our [Complete Guide to Industrial Cellular Modems & Routers].


